The Day I Almost Lost $12,000 to a Starbucks Email
I was sipping my morning coffee, half-awake, when I saw it.

An email from “Starbucks Rewards” thanking me for my recent purchase and offering a $50 gift card for filling out a quick survey. The logo looked perfect. The font was right.
It even addressed me by my nickname “Hey Akshay” which made me pause because howdid they know?
The Day I Almost Lost $12,000 to a Starbucks Email
I clicked.
For three terrifying seconds, I stared at a fake login page that looked identical to the real Starbucks app. Then my phone buzzed.
It was my bank, asking if I had just attempted to transfer $12,000 to an account in Estonia.
No, I hadn’t.
That was two years ago. I was lucky. My bank’s fraud algorithm caught the transaction in time. But that 10-second mistake taught me more about cybersecurity than a decade of IT articles ever could.
And if you’re reading this thinking, “I’m too smart to fall for that,”well, that’s exactly what I thought too.
The Problem with Being “Careful”
We treat cybersecurity like physical security. We picture hooded figures in dark rooms typing furiously, targeting specific high-value victims. But modern cybercrime isn’t Ocean’s Eleven.
It’s a conveyor belt.
Hackers don’t target you personally. They automate. They send millions of phishing emails daily, knowing that if only 0.1% of people click, that’s still thousands of compromised accounts
.The Day I Almost Lost $12,000 to a Starbucks Email
You’re not being hunted; you’re being harvested.
After my Starbucks incident, I spent six months studying how these attacks work. I interviewed a former black-hat hacker turned security consultant (who asked me to call him “Alex” for obvious reasons).
What he told me changed everything:
“We don’t hack computers,” Alex said. “We hack trust. Technology is just the delivery mechanism.”
What I Changed That Week (And What You Should Change Today)
I didn’t overhaul my entire digital life. I’m not a cybersecurity professional I’m a marketing writer who likes video games and forgets to update his apps. Instead,
I implemented what I call the “Triple Lock” method: three simple habits that take less time than brewing coffee but create exponentially more security.
The Day I Almost Lost $12,000 to a Starbucks Email
- The Password Manager Confession
I used to be the guy who used the same password for everything, with slight variations. Netflix2025! became Netflix2026! on January 1st. Clever, right?
Wrong.
When I finally audited my accounts after the phishing attempt, I discovered I’d been using a password that appeared in three different data breaches. My “secure” banking password was identical to my long-defunct Neopets account from 2007.
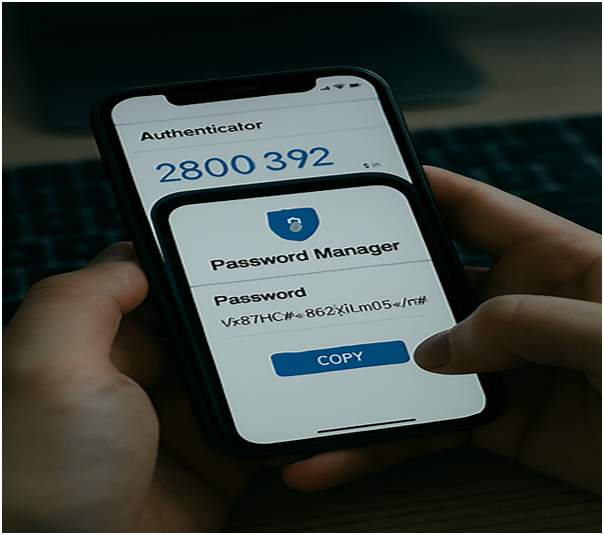
The fix: I downloaded Bitwarden (free) and spent one rainy Saturday changing every password to 20-character randomized strings.
Was it tedious? Absolutely.
But now when a service gets breached and they will—I sleep soundly knowing that password leads nowhere else.
- Two-Factor Authentication: The Annoyance That Saves Lives
I used to hate 2FA. That extra 10 seconds of grabbing my phone, squinting at a code, typing it in
it felt like digital friction, unnecessary speed bumps on the information superhighway.
Then Alex showed me the math. Enabling 2FA on your accounts blocks 99.9% of automated attacks. Not 50%. Not 90%.
Ninety-nine point nine.
Now I treat 2FA like my seatbelt. Sure, it’s slightly inconvenient 99% of the time when I’m just driving to the grocery store. But that 1% moment when I need it? It’s the difference between a scary story and a financial catastrophe.
3. The “Pause Before You Type” Rule
This one costs nothing and requires no technical skill.
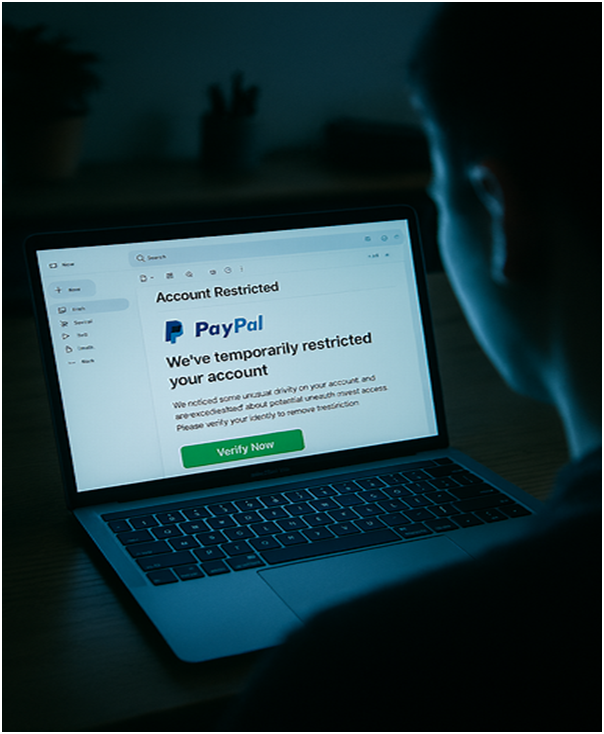
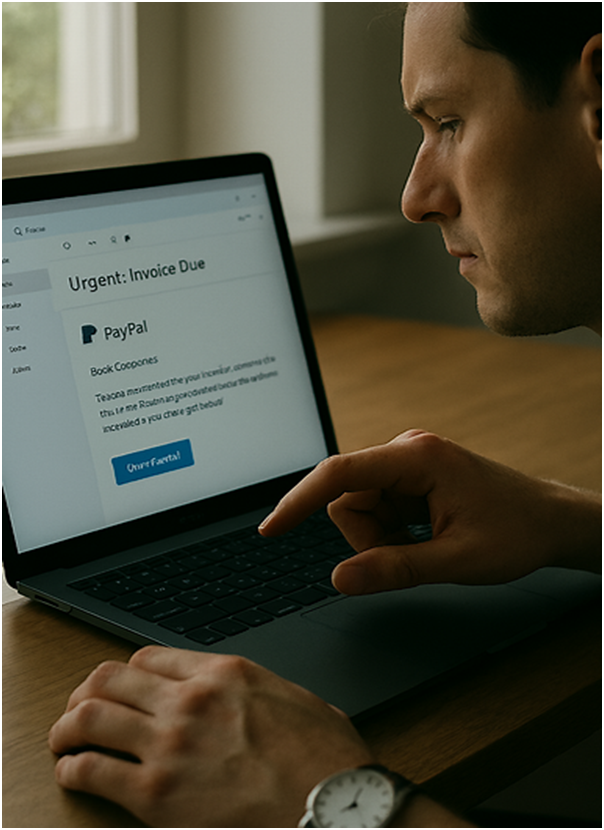
Hackers exploit what psychologists call “amygdala hijacking” triggering fear or excitement so you act before you think. Urgency is their weapon. “Your account will be deleted in 24 hours!” “Suspicious activity detected!” “You’ve won an iPhone!”
Now, when any email or text demands immediate action, I enforce a 60-second rule. I close the message. I open a new browser window. I manually type the website address (amazon.com, not the link in the email). I check my account the long way.
That minute of inconvenience has saved me from two sophisticated phishing attempts this year alone. One pretended to be from my CEO. Another claimed my daughter’s school lunch account was overdrawn. Both looked flawless. Both were traps.

The Bigger Picture: You’re Not the Product, You’re the Perimeter
Here’s what keeps me up at night now: we’ve built a digital society where the individual is the last line of defense. Companies collect our data with minimal protection. Apps demand permissions they don’t need. We trade privacy for convenience because the alternative feels like living off-grid.
But here’s the hopeful part: cybersecurity isn’t about being paranoid. It’s about being prepared.
Think of it like locking your front door. You don’t expect to be robbed tonight, but you still turn the key. Not because you live in fear, but because you value what’s inside.
Your digital life your photos, your financial history, your identity—is worth that same basic diligence.
Not because hackers are geniuses, but because, like me that Tuesday morning with my coffee, we’re all just one distracted moment away from a very expensive mistake.
Your Three-Minute Challenge
Before you close this tab, do this:
- Check your passwords. Go to Have I Been Pwned and enter your email. If you see red, change those passwords today.
- Enable 2FA on your email and bank accounts right now. Yes, it’ll take three minutes. Yes, it’s worth it.
- Tell someone. Forward this to that one friend or parent who still uses “password123” or clicks every “You’ve got a package!” text. Cybersecurity is herd immunity the safer your circle, the safer you are.
The hackers aren’t going anywhere. But neither is your ability to outsmart them.
You don’t need to become a tech expert. You just need to be slightly harder to hack than the next person.
And trust me: that gap between “easy target” and “slightly harder target”? It’s the difference between a hacker moving on to the next email… and you writing a blog post about the time you got lucky.
Stay safe out there.
— AKSHAY BANNUR
P.S. If you’re wondering what happened to that $12,000—the bank reversed the transfer, but not before I spent three weeks on the phone with fraud departments and changed every account number I own.
Sometimes the best security lesson is the one that scares you just enough to change, but not enough to ruin your life. I got lucky. Don’t wait for luck.